Installing vsftpd on CentOS 7
Use the yum package manager to install vsftpd.
yum -y install vsftpdCreating an FTP User and Directory
While vsftpd creates a default ftp system user, it's recommended to create a dedicated user for security and management.
1. Create a Dedicated User
Create a user named ftpuser with a home directory of /var/ftp/pub and disable shell access.
adduser -d /var/ftp/pub -g ftp -s /sbin/nologin ftpuser2. Set the User Password
passwd ftpuser3. Configure the User Access List
Edit the user list file to add the new user. The behavior depends on the userlist_deny setting in vsftpd.conf.
vi /etc/vsftpd/user_listAdd ftpuser to the end of the file.
4. Configure Chroot Directory Locking
Edit the chroot list file to specify users restricted to their home directory.
vi /etc/vsftpd/chroot_listAdd the username ftpuser to the file.
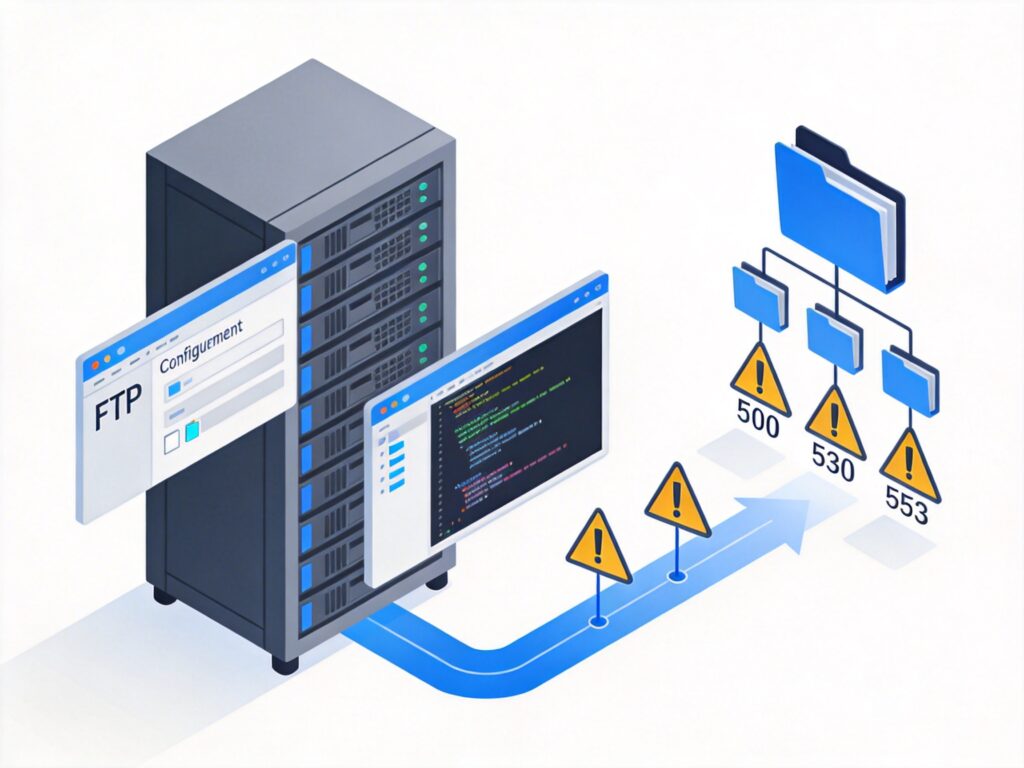
Modifying the vsftpd Main Configuration File
The main configuration file is /etc/vsftpd/vsftpd.conf. Key settings:
anonymous_enable=NO: Disable anonymous login.local_enable=YES: Allow local user login.write_enable=YES: Allow write operations.local_umask=022: Default permission mask for files created by local users.chroot_local_user=YES: Restrict all local users to their home directory.chroot_list_enable=YES: Enable the chroot user list.chroot_list_file=/etc/vsftpd/chroot_list: Path to the chroot list file.userlist_enable=YES: Enable the user list feature.userlist_file=/etc/vsftpd/user_list: Path to the user list file.userlist_deny=NO: Only allow users listed inuser_listto log in (whitelist mode).
Save the file after making changes.
Fixing PAM Authentication (Resolving 530 Login Incorrect Error)
Edit the PAM configuration file /etc/pam.d/vsftpd. A common secure configuration is:
#%PAM-1.0
session optional pam_keyinit.so force revoke
auth required pam_listfile.so item=user sense=deny file=/etc/vsftpd/ftpusers onerr=succeed
# Comment out pam_shells.so to allow users with shells like /sbin/nologin
#auth required pam_shells.so
auth required pam_nologin.so
auth include password-auth
account include password-auth
session required pam_loginuid.so
session include password-authThe key step is commenting out the auth required pam_shells.so line; otherwise, users with /sbin/nologin shells cannot authenticate.
Resolving 500 OOPS: vsftpd: refusing to run with writable root inside chroot() Error
For security, vsftpd 2.3.5+ prevents chrooted users from having write permissions on their home directory. Two solutions:
Method 1: Remove Write Permission from Home Directory (Recommended)
Create a subdirectory (e.g., upload) for uploads and ensure the home directory itself is not writable.
mkdir /var/ftp/pub/upload
chown ftpuser:ftp /var/ftp/pub/upload
chmod a-w /var/ftp/pubMethod 2: Allow Writable Chroot Directory (Less Secure)
Add the following line to /etc/vsftpd/vsftpd.conf:
allow_writeable_chroot=YESNote: Method 2 reduces security; use only in specific scenarios.
Resolving 553 Could not create file Error
This error is usually due to insufficient write permissions on the target directory. Ensure the FTP user has write access to the upload directory.
chown -R ftpuser:ftp /var/ftp/pub/upload
chmod -R 755 /var/ftp/pub/uploadManaging vsftpd Service on CentOS 7
- Start service:
systemctl start vsftpd - Stop service:
systemctl stop vsftpd - Restart service:
systemctl restart vsftpd - Check status:
systemctl status vsftpd - Enable at boot:
systemctl enable vsftpd
Firewall and SELinux Configuration
1. Firewall
If the system firewall (firewalld) is active, allow the FTP service (port 21) and the passive mode port range.
firewall-cmd --permanent --add-service=ftp
firewall-cmd --reload2. SELinux
If SELinux is in enforcing mode, adjust the boolean to allow FTP access to user home directories.
setsebool -P ftp_home_dir onFor non-standard directories, additional file context labeling may be required.
FTP Client Connection and Testing
Use an FTP client (e.g., FileZilla) or the command-line ftp tool to test the connection with the correct username, password, and server address.
Tip: In modern networks, consider using more secure alternatives like SFTP (over SSH) or FTPS (FTP over SSL/TLS) instead of plaintext FTP.